Understanding Hash Cryptography In Blockchains Part 2: Five Requirements of a Cryptographic Hash Function

Application Security | Test Automation
In Part One , we saw what a cryptographic hash function is and in this short five minute introduction to Blockchain, we saw how it used in a Blockchain. Today, I will try to explain the five requirements of a good cryptographic hash function.
A good cryptographic hash function must possess the following five properties:
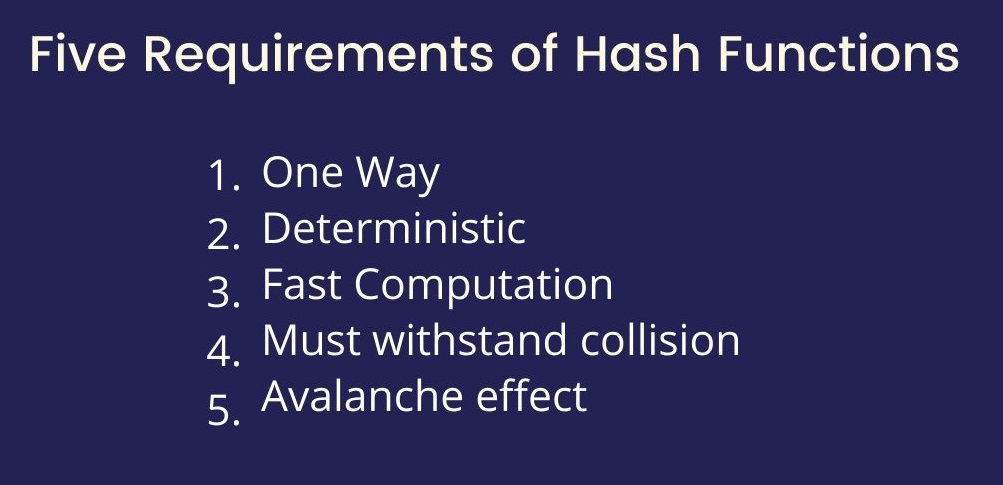
One way
A cryptographic hash function must always be one way. That is, it should be possible to find the hash from an input easily. But, the reverse must not be possible. By no means should the input be recovered from the hash. This one way functionality of hashes is the reason why passwords are usually hashed before they are stored in the database.
So even if someone manages to get access to the database, they still won’t be able to reverse the hash.
Deterministic
A cryptographic hash function must be deterministic. For a given input value, the output must always give the same hash value if passed through the same cryptographic hash function. In addition, two copies of the same document should also always give the same hash when passed through the same cryptographic function.
Fast Computation
The cryptographic hash functions undergo a number of complex mathematical computations before they produce the hash. These computations make the hash one way, so they are important and can’t be ignored.
However, computers must also be able to perform these complex mathematical calculations involved in producing the hash in a short period of time. This property of producing the hash in a short time is also known as the hash functions being computationally efficient.
Must withstand collisions
A collision is a situation when the hash function gives the same output value for two different inputs. The perfect analogy for this is having two human beings with same fingerprints. The probability of two human beings having the same fingerprint is one in 64 million. Similarly, no two unique inputs should produce the same hash as output. This property of a hash function withstanding collisions is very important for blockchain based applications.
Avalanche Effect
The hashes generated from an input must not have any visible pattern of hash generation. This is because no user should be able to find a hidden way of guessing the hash; else they will be able to break the hash function easily. And so, for every single bit change in the input, the output hash should change completely. This is called the Avalanche effect.
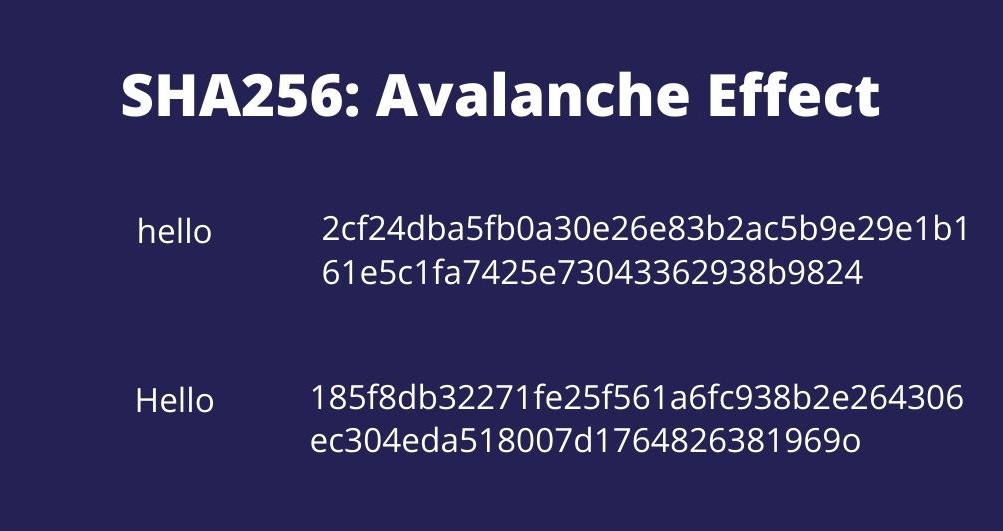
So, “hello” and “Hello” will produce completely different hashes without showing any pattern.
These are the five important characteristics of any good cryptographic hash function. I hope you enjoyed this post.
Feel free to reach out on Twitter(@ar6aaz) or Instagram(@theblockchainblog)
Until next time.